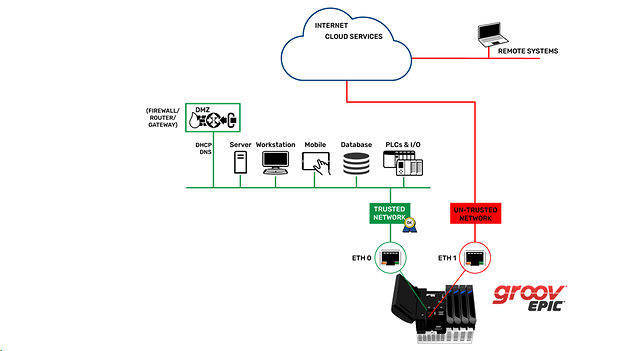
The dual Ethernet ports feature of groov EPIC is one of the strongest security aspects of the system.
It would pay to look closely at your network and how the two ports are currently connected (if at all).
You should setup your groov EPIC to only have ETH port 0 connected to your trusted network and ETH port 1 to connect to your untrusted network.
A trusted network is any network where you know exactly who has access to it, for example, an IT-managed corporate network.
An untrusted network is any network where you don’t know who has access to it, like the internet.
It is important to note that groov EPIC does not route traffic between network interfaces. It does not have router functionality. This adds to security as each port is isolated from the other. Access is controlled via the firewall.
Speaking of the firewall, you can adjust the open ports and the network they use, so be sure to check the settings and make any adjustments you feel fit.
Here are some notes for best practices for groov EPIC network security.
Networks
• Configure your groov EPIC to use the ETH0 Ethernet network interface for your trusted network.
• Use ETH1 for any untrusted network. Configure exceptions in the system’s firewall only if required for your application.
• Configure the system’s firewall in groov Manage to close all unneeded network ports on all network interfaces.
Users
• Don’t simply make every user an Admin. Use the different level settings to set each user to the right privileges.
• Have all your users create long and difficult passwords or better still use a passphrase, and don’t write them down anywhere.
• Use a VPN if you require remote network connections over untrusted networks.
• To prevent unauthorized access to the groov EPIC processor, always log out of any ID that has
administrator privileges.
• If you are running your groov View HMI on an external monitor, always put it in Kiosk mode so that only groov View is accessible.
Other Best Practices
• If you need a completely closed system (for example, if you are an OEM using groov EPIC in your machine), after you have finished development, disable all ports in the firewall and unplug any Ethernet cables.
If someone attempts to connect an Ethernet cable to the EPIC to try to access the system from their computer, the ports will be closed and all network access will be denied. Only an authorized user with administrator privileges can access groov Manage through the built-in display to reopen needed ports and gain network access.
• Whenever possible, use authenticated and encrypted outbound data communication methods. For example, use MQTT to publish data to an MQTT broker. Outbound data communication methods help you:
– Reduce open inbound network ports
– Eliminate man-in-the-middle exploits
– Prevent exposing sensitive credentials over the network
We will be putting together these notes and more in a security learning lesson on https://training.opto22.com/ as soon as we can.